Overview
This tutorial explains how to configure Incydr to use single sign-on (SSO) with Shibboleth.
This article assumes you are already familiar with SSO and the SAML standard. For more information about how Incydr implements SSO, see our Introduction to single sign-on.
Single sign-on (SSO) for Incydr
• These SSO instructions apply only if you access Incydr directly via a console.*.code42.com URL (typically for SSO configured before September 2025).
• If you access Incydr from the Mimecast Administration Console after signing in at login.mimecast.com, these instructions do not apply to you (typically for SSO configured after September 2025).
• Directory services information, however, applies to all Incydr environments.
Considerations
External authentication systems
Our Technical Support Engineers can help with authentication issues caused by interaction with Incydr products. However, troubleshooting authentication issues outside your environment is beyond the scope of our Technical Support Engineers. For assistance with external authentication systems, contact your authentication vendor.
- To use this functionality, you must be assigned the Identity Management Administrator role.
- Incydr usernames must match SSO usernames. How you accomplish this depends on how you deploy agents.
- Incydr supports service provider-initiated SSO but does not support identity provider-initiated SSO. Therefore, users cannot sign in to your environment from the identity provider's website or application, but instead must log in using a browser bookmark.
- SSO provides user authentication but does not provide user management. Set up SCIM provisioning or use the Incydr console to manage users.
- Incydr does not support Single Logout (SLO). Users must sign out of the identity provider to end their single sign-on session.
- The Incydr console expects SAML assertions to be signed. To configure Incydr to support advanced SAML request configurations, see Set SAML attributes for SSO.
Before you begin
Verify identity provider configuration
- Make sure the SSL certificate of your SSO identity provider has been signed by a trusted Certificate Authority (CA).
- Make sure you have administrative access to the identity provider or have contact with an identity provider administrator.
Verify network configuration
- Configure your private network, Internet, and VPN settings to allow client devices to communicate with your identity provider on port 443. Test client connectivity to the identity provider before you proceed.
- If you want to use URL-based metadata exchange to configure Incydr and the identity provider to work together, make sure two-way communication is available between them on TCP port 443. If two-way communication is not available or not allowed, you must download the identity provider's metadata file and make it accessible to Incydr.
- Confirm the required ports with your identity provider to determine if custom ports are being used.
Determine whether you need to configure multiple Incydr tenants
Before you begin configuring SSO, consider whether your company has more than one tenant that you need to connect to your SSO identity provider. Large companies and organizations may have separate, dedicated Incydr cloud instances (or "tenants") in use by different groups or departments.
If you have more than one Incydr tenant to connect to your SSO identity provider, you need to obtain an entity ID URL for each tenant. An entity ID is a unique string that identifies a specific tenant to your SSO identity provider. The tenant-specific entity ID URL is composed of the Incydr cloud domain followed by the tenant ID, and can be found in the service provider metadata URL file in each tenant. For example:
"entityId": "https://example.com/42424daa-424c-4e42-42c4-c424242420d4"
Step 1: Add an authentication provider
Follow the steps below for adding the authentication provider's metadata URL to the Incydr console.
Shibboleth
Use the Shibboleth metadata URL provided by your institution.
-
Sign in to the Incydr console.
- Navigate to Administration > Integrations > Identity Management.
- Click Add authentication provider.
The Add Authentication Provider dialog appears.
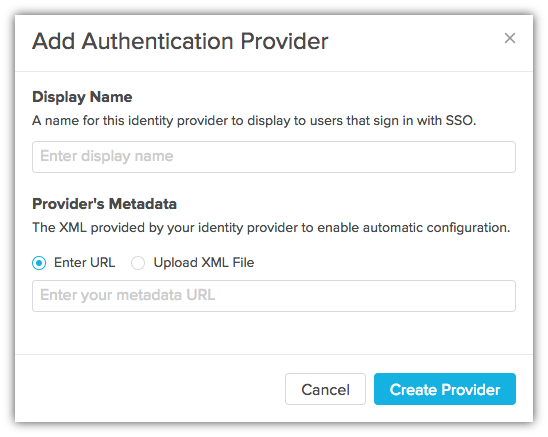
- In Display Name, enter an identity provider name to display to users who sign in with SSO.
If your environment provides more than one SSO identity provider, users see a list of providers to choose from. They must select the provider configured for their Incydr organization.
- In Provider's Metadata, ensure that Enter URL is selected and paste the URL for the identity provider metadata XML file, or click Upload XML File and select the XML file for upload.
Custom domains are not supported
When entering the URL for the XML metadata file, custom domains are not supported. You must use the standard domain of your identity provider.
- Click Create Provider.
Authentication provider settings appear.
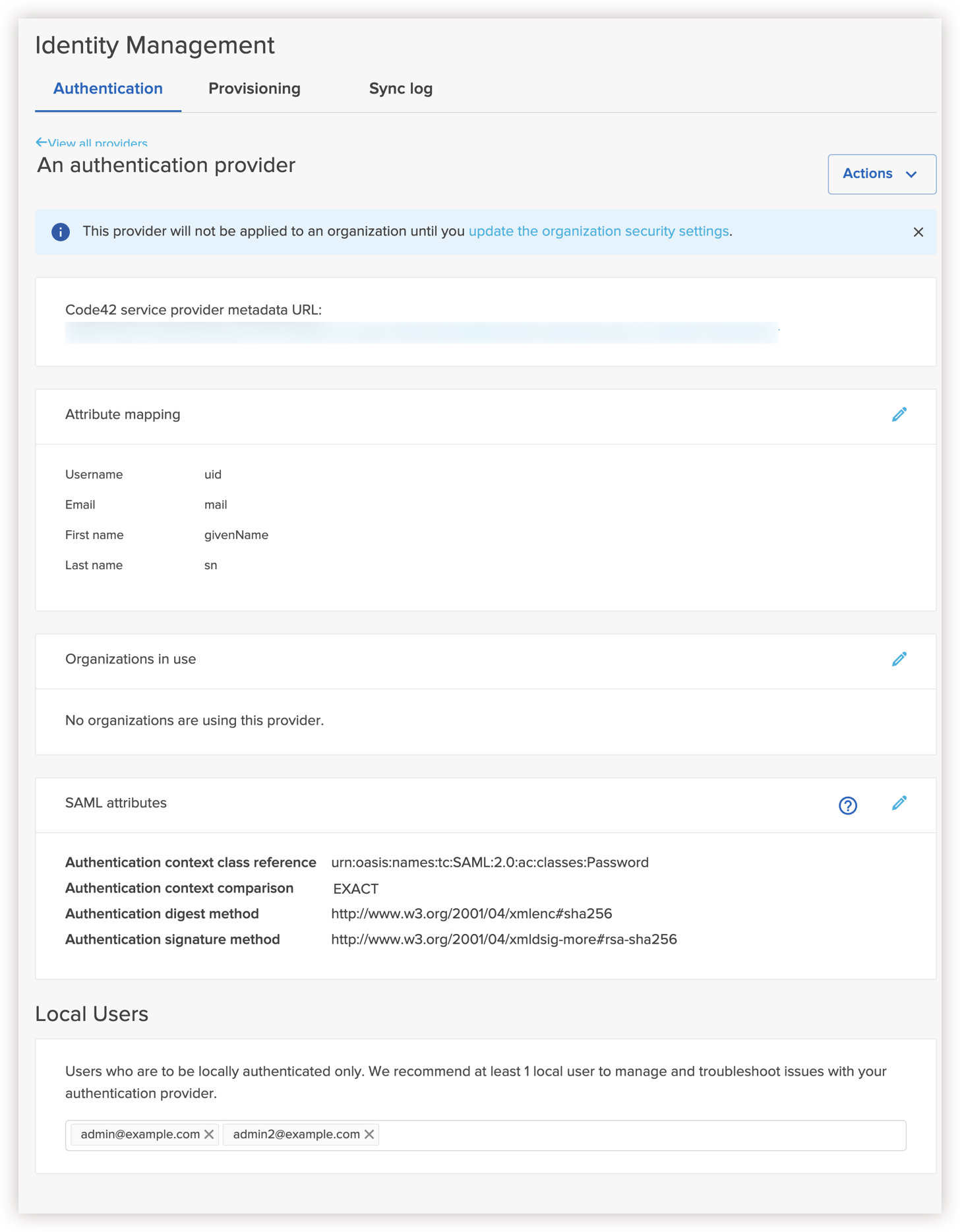
Provider information message
Note the following message on the dialog:
This provider will not be applied to an organization until you update the organization security settings.
Do not apply this authentication provider to organizations yet. You will apply this provider to a test organization and to production organizations in later steps.
- If you choose not to use default mapping, you can use Attribute Mapping to customize mappings between Incydr user attributes and authentication provider SSO assertion attributes.
- Click Edit.

- Deselect Use default mapping.
- Configure mapping settings for each Incydr user attribute.
Each field supports up to 128 characters.
-
Username: Specify the identity provider's name ID or attribute that maps to the Incydr username.
- Select Use nameid to use the identity provider's name ID.
- Select Use attribute tag to enter a custom identity provider attribute.
-
Email (Use nameid only): Enter the identity provider attribute that contains user email addresses.
-
First Name: Enter the identity provider attribute that contains user first names.
-
Last Name: Enter the identity provider attribute that contains user last names.
-
Click Save.
-
(Optional) Local Users displays the current user. If there are any other users you want to exempt from using this authentication provider to log in, enter them here.
Step 2: Prepare Shibboleth
There are two ways to exchange metadata between your environment and the Shibboleth identity provider:
- If two-way communication is possible between Shibboleth and the Incydr cloud, use URL-based metadata exchange. This method periodically retrieves metadata from a given URL and stores the metadata file locally, so it can be used if the remote source is unavailable.
- If two-way communication is not available, use file-based metadata exchange.
For more information about adding a service provider to Shibboleth, see the Shibboleth documentation.
Shibboleth option A: URL-based metadata exchange
Configure your environment as a file-backed HTTP metadata provider.
- Make sure the Shibboleth identity provider can access the service provider metadata URL.
Find your environment's metadata URL under Administration > Integrations > Identity Management on the Authentication Providers tab.
- Configure your Shibboleth identity provider to accept authentication requests from your environment.
- Edit the file
${Shibboleth}/conf/relying-party.xml.
- Add or modify the
MetadataProvider element for your environment.
<MetadataProvider xsi:type="FileBackedHTTPMetadataProvider" xmlns="urn:mace:shibboleth:2.0:metadata"
id="Code42_Environment"
metadataURL="https://console.us.code42.com/api/SsoAuthSpMetadata?registrationkey=xxxxxxxxxxxxxxxx"
backingFile="/tmp/idp-metadata.xml" />
Set the following values by modifying the text between the quotes:
-
id: A name for your environment.
-
metadataURL: Your environment's service provider metadata URL.
-
backingFile: The path to the backup copy of the service provider metadata file on the identity provider.
Shibboleth option B: File-based metadata exchange
Configure Incydr as a filesystem metadata provider.
- Download the service provider metadata file, and upload it to the identity provider.
The service provider metadata file is located in the Incydr console in the authentication provider details.
- Configure your Shibboleth identity provider to accept authentication requests from Incydr.
- Edit the file
${Shibboleth}/conf/relying-party.xml.
- Add or modify the
MetadataProvider element.
<MetadataProvider xsi:type="FilesystemMetadataProvider" xmlns="urn:mace:shibboleth:2.0:metadata"
id="Code42_Environment"
metadataFile="/path/to/my/metadata.xml" />
Set the following values by modifying the text between the quotes:
-
id: A name for your environment.
-
metadataFile: The path to the service provider metadata file on the Shibboleth identity provider.
Configure your Shibboleth identity provider to sign assertions
The Incydr console expects assertions to be signed. See Shibboleth's documentation for more information.
- Edit the file
${Shibboleth}/conf/relying-party.xml.
- Add or modify the
ProfileConfiguration element, for example:
<RelyingParty id="urn:example.org" provider="https://idp.example.org" defaultSigningCredentialRef="ExampleOrgCred">
<ProfileConfiguration xsi:type="saml:SAML2SSOProfile" signAssertions="always"/>
</RelyingParty>
- Set the
signAssertions attribute to always.
Step 4: Test SSO authentication
Step 5: Configure organizations to use SSO
-
Sign in to the Incydr console.
- Navigate to Administration > Integrations > Identity Management.
- Select the authentication provider.
- Click Edit
 next to Organizations in use.
next to Organizations in use.
- Select organizations to use the authentication provider for SSO.
If applicable, select the Inherits settings to identify whether an organization inherits the setting from its parent organization. To enable SSO for all organizations, select the top-most organization. (Note that you can also use an organization's settings to select an authentication provider to use for SSO.)
- Click Save.
Step 6: Add new users that sign in with SSO
Option A: Add users in the Incydr console
Use the Incydr console to add users to an organization that uses SSO.
- Verify that the users in the organization exist in the SSO identity provider used by the organization.
- Make sure that the environment usernames match the SSO usernames.
Option B: Deploy agents
What to expect
Reduced authentication prompts
When users sign in with SSO, they do not need to re-enter credentials for subsequent authentication attempts until the SAML authentication token expires. A SAML token applies to an application rather than a device, which means that a user might need to enter credentials again when signing into a different app.
For example, the single sign-in process differs whether users sign in to the Incydr console or agents:
-
Incydr console: When users sign in to the Incydr console, they are redirected in the web browser to sign in to their SSO identity provider. As soon as they sign in to their identity provider, the Incydr console launches.
-
Backup agent: When users sign in to agents, following message appears: "To complete the sign in process, go to your web browser. This screen updates automatically once login is successful." A web browser window is automatically opened so they can complete the sign-in process in their SSO identity provider. As soon as they sign in to their SSO identity provider in the provided web browser window, the agent launches.
Losing access to an identity provider
Backup agent only
If a user loses access to the identity provider, agents continue to back up, uninterrupted.
Troubleshooting
Expired SSL certificate
If the SSL certificate for your identity provider expires, follow these steps to delete and re-add the provider:
- In the Incydr console, select Administration > Integrations > Identity Management.
- From the Actions menu, select Delete this authentication provider.
- Follow the steps above to re-add the provider with a new XML metadata file that applies to the new certificate.
External resources
Related topics
Comments
Please sign in to leave a comment.